
Foundation to Blueprint – Building Your Cybersecurity Stronghold
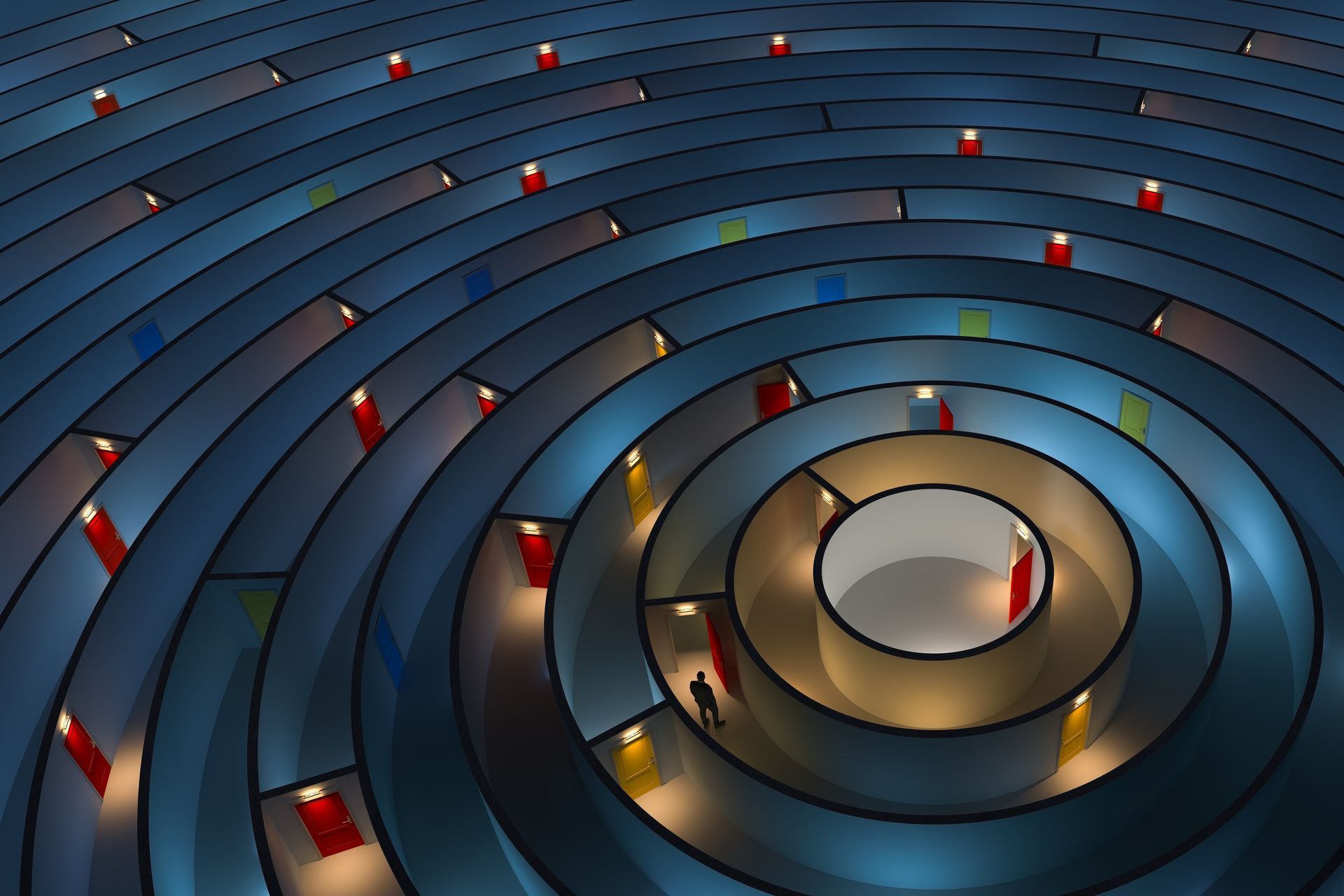
Think about building a house. You start with a strong foundation that is engineered to support a framework, walls, and all the things that will be built upon it, as well as the things that will be brought in. And of course, protect the people who live in it.
The same is true with cybersecurity – your network starts with a foundation and then you build the infrastructure (the blueprint for wiring, plumbing, walls and a roof). But everything must be built upon a strong foundation so that people can operate in the network securely.
With the velocity of hacks increasing, especially as more people continue to work remotely (many without a proper security foundation or knowledge of what that even looks like), the new landscape is creating a target-rich environment for bad actors. In fact, Accenture reports that 68% of business leaders feel their cybersecurity risks are increasing.
Small and mid-sized businesses (SMB) may be more at risk. SMBs are less likely to have a Chief Information Security Officer (CISO) in place and more likely to have outdated cybersecurity solutions. Many times, smaller businesses can struggle with identifying those hard-to-find vulnerabilities, simply because of the time it takes, and the expertise it requires.
The following three-step roadmap can help ensure your team stays ahead of attacks and is better equipped to outpace bad actors:
- Threat & Vulnerability Management: This really is all about an arms race. From identification of vulnerabilities to the ability for hackers to exploit before your security team can identify the threat and fix it, or even know about it. It’s very important that your security team are threat hunters who scan and proactively check for security software for threats and basically knows how to get the most out of your cybersecurity solutions and protect against bad actors. It is crucial that you monitor the products installed across your network to ensure peak performance. Subscribing to security intelligence reports is also key to maximizing the impact of your security technology products and their patch or configuration availability. That means a consistent cycle of monitoring, understanding trending threats and patching maintenance is essential to ensure you are getting the most out of the solutions you pay for. We can help your team map out a plan.
- Configuration & Patch Management: This is the other side of the coin of your threat and vulnerability management program. Monthly, proactive patching, with the ability to immediately implement security patching, is absolutely mandatory! Make sure vendor security and product patches are applied expeditiously to both those IT systems that are internet facing, as well as internal. IT solutions that are no longer supported by vendors create a huge, unnecessary risk. Do you have the ability to patch your security solutions as soon as a new threat is identified? We can help.
- Endpoint Protection: If you have been using the same old anti-virus (AV) solution for the last couple years, it is time to upgrade your tool kit by moving away from signature-based detection (antivirus) and start using behavior-based monitoring. The AV market has converged and matured, including the integration of EPP (endpoint protection) with EDR (endpoint detect and response). EDR is based on the premise that at some point an infection is going to occur. The next generation EPP improves the ability to identify indicators of attack, investigate with real-time forensics, sophisticated visualizations and perform remediation. We can help your team identify the right upgrade or new product for your business.
We can’t emphasize enough the vital importance of a strong cybersecurity foundation, which we’ve covered in recent
blogs. As the average cost of a data breach is estimated to be almost $3.9 million, it only makes sense to spend a little now to invest in your cybersecurity stronghold. We can help you get started, or help you accelerate your cybersecurity journey.
Contact us today.
Author:
Erich Escobar 2021
Search Post
Category
Recent Posts


Share Post
